Deceiving domain - smartpackagetracker.com
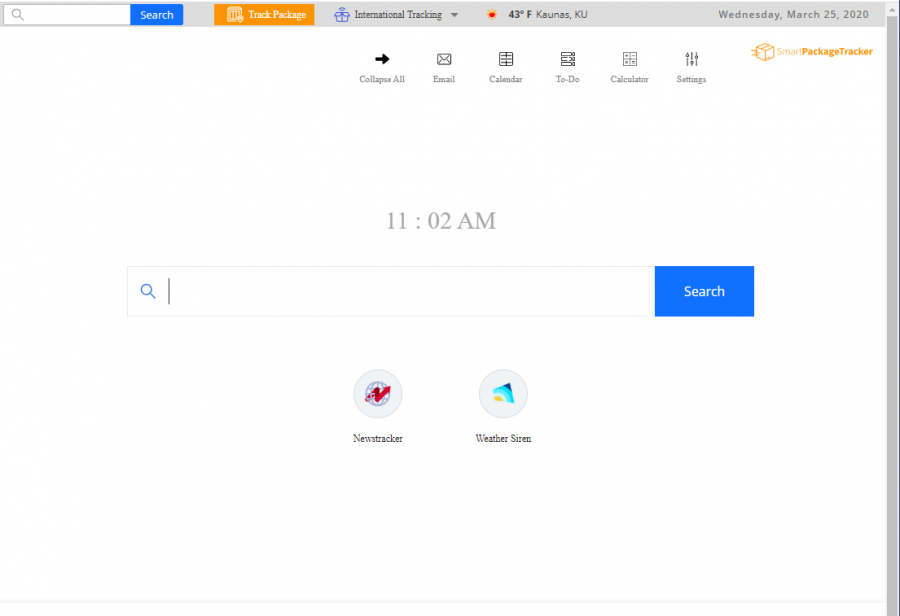
Smartpackagetracker.com is the domain name of a browser hijacker that performs unexpected changes on the browser's default search engine, homepage, and new tab URL zone. The app then tries to attract a bigger number of users by providing people with package tracking, weather watching, and news catching features.
Also, Smartpackagetracker.com can include various extensions, plug-ins, and toolbars into the browser's settings. Then, you are likely to get redirected to affiliate domains some of which might appear to be potentially dangerous and receive loads of advertising content that offers misleading deals.
Furthermore, Smartpackagetracker.com is known for its ability to collect browsing and device-related information. For this aim, the hijacker employs web beacons or HTTP cookies and includes them in the hijacked web browser app. Then, the developers are able to see what type of machine you are using, your IP, and online activities.
Browser hijackers such as Smartpackagetracker.com are mostly never installed intentionally and come through bundled software that the user downloads from secondary sources such as softonic.com or download.com. Also, you can receive the PUP from a click on an infectious link, ad, or fake software update.
| Name | Smartpackagetracker.com |
|---|---|
| Type | Browser hijacker/PUP |
| Tasks | Hijacking the default engine, homepage, and new tab bar, loading advertising content during browsing sessions, redirecting the user to sponsored pages, collecting non-personal information |
| Distribution | PUPs can get downloaded by employing software bundling, clicking on an infectious link, advert, or false update |
smartpackagetracker.com violations
2CR-004: The app completes changes on the browser's engine, homepage, and new tab bar