Deceiving domain - see-me.xyz
See-me.xyz is a participant of a social engineering attack that seeks to steal sensitive information on users' devices. The domain is just one of dozens that were used to promote an alleged greeting card scheme, where users can create seemingly harmless greetings and direct them to family members, friends, and others. In most cases, See-me.xyz links are being distributed via social media platform message apps, such as Facebook Messenger, WhatsApp, Discord, and others, which includes the following message (along with a few emojis):
Touch This Red Dot
I am send you a surprise message. Open this
As soon as the See-me.xyz link is clicked, users are redirected to a site where a background script is run. During this time, the threat inserts malicious processes into legitimate Windows APIs, which allows it to elevate its permissions. As a result, users who click the link can be exposed to sensitive information theft, such as passwords, emails, etc. Additionally, See-me.xyz redirects and links will be populated to the victim's friend list via the social media platform, delivering malware to others.
| Name | See-me.xyz |
| Type | Redirect virus, malicious background script |
| Related | Open-fast.com, Wish-you.co |
| Aim | Steal sensitive user information and deliver malicious phishing message via social media platforms to other users |
| Activities | Injects malicious processes into legitimate Windows APIs - attack vector known as hooking |
see-me.xyz violations
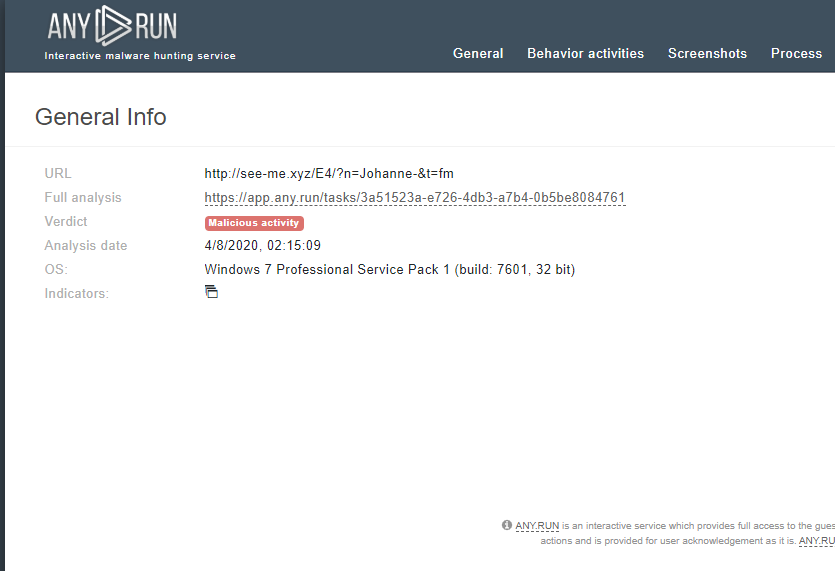
2CR-015: AnyRun analysis detected http://see-me.xyz as malicious