Once again hackers are exploiting coronavirus pandemic fears to benefit financially
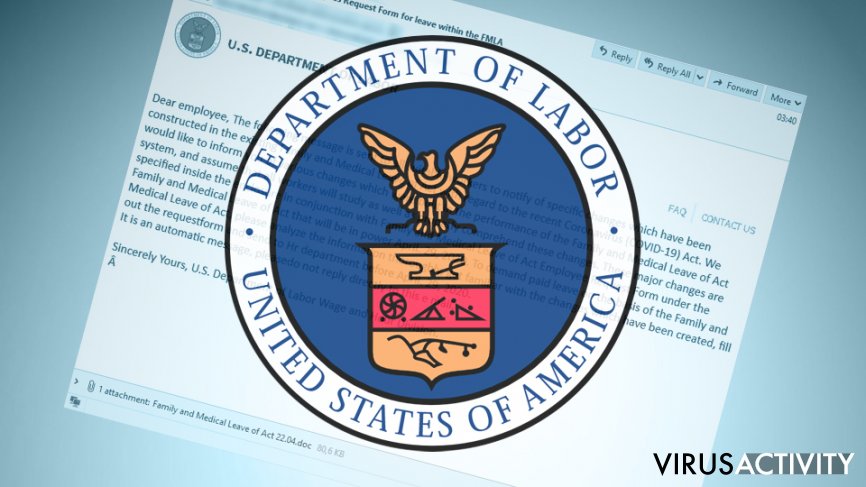
Security researchers from IBM X-Force have uncovered a new campaign that spreads TrickBot banking malware – threat actors are sending malicious spam emails that seem to come from the U.S. Department of Labor. Inside the email, victims are claimed to be entitled to medical leave benefits during the COVID-19 pandemic under the changes made to the Family and Medical Leave Act (FMLA).
The attackers claim that users should familiarize themselves with changes made to FMLA and fill in the form that is meant to be sent back to the U.S. Department of Labor Wage and Hour Division. The attachment, which is a DocuSign-type MS Office word document, begins the infection routine of the well-known banking Trojan TrickBot.
As it is common for the current COVID-19 situation, multiple cybercriminal gangs began intensifying their operations, as many people are forced to work from home. Due to this, security researchers saw a spike in coronavirus-related spam emails that are trying to abuse the development, relief payments, and other relevant trends related to the pandemic. According to researchers, a total of 1.5 million of COVID-19-themed phishing emails are sent every day, infecting users with data-stealers, ransomware, and other malware in the process.
Malicious macros exploited to deliver the TrickBot payload
Phishing emails have been one of the most used tactics for malware delivery, and TrickBot is not an exception. Malicious actors often exploit human fears or other psychological factors with the help of social engineering and the most recent trends that many are well aware of. Unfortunately, many fewer people are aware of data-stealing malware and its propagation techniques, which results in thousands of infections daily.
In the sample analyzed by IBM researchers, the subject line read, “This is the changed Employees Request Form for leave within the FMLA.” The body of the email included the U.S. Department of Labor logo and the explanation about the alleged changes in FMLA, as well as the attachment titled US-DoL.eml. Inside, users could find three attachments: “us-logo.png,” “faq.png,” and Family and “Medical Leave of Act 22.04.doc.” While the first two are insignificant, the latter .doc file is the one that carries TrickBot.
Once the “Allow content” on the document is clicked, a malicious macro will launch VB scripts in order to download the main payload from the attackers' servers and infect the host machine with TrickBot.
TrickBot is operated by an experienced cybercriminal group
TrickBot is not your average Trojan. This threat was first introduced back in 2016 and immediately started targeting medium to small businesses, along with regular consumers in the U.S., UK, Australia, and other countries. Malware is operated by experienced and sophisticated hackers, which explains its prevalence around the world. Besides, TrickBot was also used in collaboration by the notorious APT (Advanced Persistent Threat) group FIN6.
TrickBot is modular malware that specializes in data capture from web browsers, digital wallets, network tools, etc., with the help of the post-exploitation tool Mimikatz. Over the years, it has been improved and upgraded several times by its operators; for example, security researchers from Trend Micro noticed a new Remote App Credential-Grabbing module in February 2019. It poses a tremendous danger to the infected, as explained by IBM researchers:
Users infected with the TrickBot Trojan will see their device become part of a botnet that can allow attackers to gain complete control of the device. Typical consequences of TrickBot infections are bank account takeover, high-value wire fraud, and possibly ransomware attacks targeting organizational networks.
Recently, Microsoft researchers dubbed TrickBot, the most prolific COVID-19 malware during the pandemic, as new campaigns are launched regularly, infecting thousands of users are organizations worldwide.

