Banking credentials stealing malware has multiple versions already and is still active
Banking Trojan malware is on the rise right now and ransomware is left in the second place since trojans are the top malware distributed via email. Emotet malware family has many versions of various Trojans, and each one of them is set to proliferate different tasks. The most common purpose of these cyber intruders is stealing credit card credentials or similar banking information from the user with the main goal of getting money. The costly virus evolved during all these years, from a standalone banking trojan to a notorious and destructive malware.
Emotet banking trojan that steals financial information and spreads by using the infected devices is on the rise right now, according to various sources. In a few days in September 2018 hundreds of new malware payloads spawned all over the world. During these attacks, companies needed to take serious actions and it is said that malware campaigns have cost up to $1 million for each organization. This particular trojan is the one that is accountable for almost 57 percent of all banking malware attacks. This type of malware affects nearly 10 percent of all organizations around the world.
Emotet malware functionality
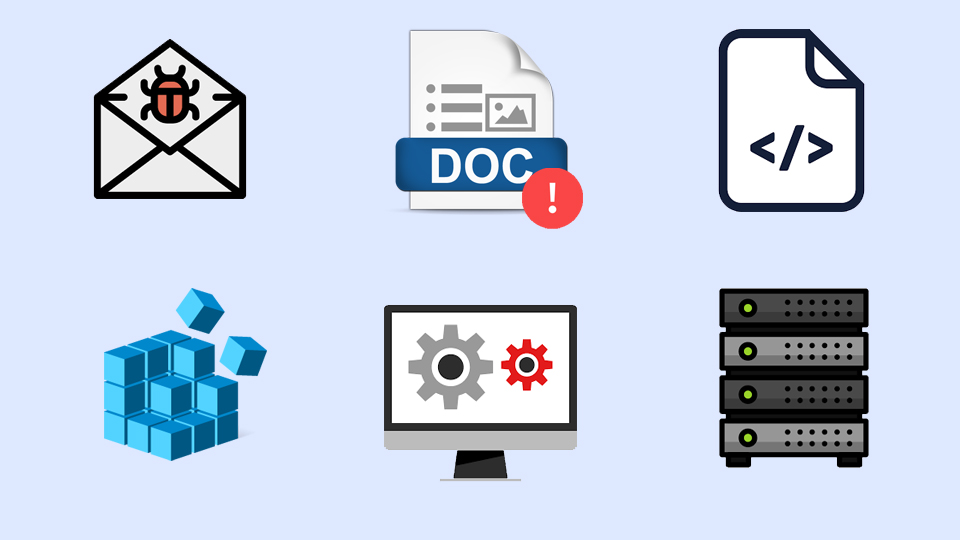
Emotet self-propagates and affects mostly networks of large businesses. It spreads via spam email attachments and links which initiate the download of malware directly on the device. When on the system, Emotet executes the module that has a list of passwords which helps to spread the malware on other devices in the same network.
This brute-force module passwords and spam email module distributes Emotet throughout the machines on the infected network. Social engineering tactics are used to create spam emails with subjects like “Invoice” or “Order information”. Also, these emails can be created with the name of a person which email account was compromised, to look more legitimate. The email contains file attachments or a link with the malicious payload. When the user opens an infected file or clicks on the link that initiates the download, Trojan.Emotet infects the system.
Trojan malware distribution ways
In the cyberthreat world, there are all kinds of malware with different spreading methods. Insecure downloads are the reason for potentially unwanted programs, but harmful malware like trojans or ransomware distributes via spam email attachments or other malware that is designed to initiate other infections. The most dangerous infections like Trojans or crypto miners work silently, and you cannot notice the intruder at first because this infiltration process is silent.
The main thing about these spam emails that people can easily notice is file attachments or hyperlinks in the email itself. Another feature people are not paying attention to is the subject of the email and the sender. Often in these email spam campaigns, hackers use well-known company names like FedEx, PayPal or Amazon, to make emails more safe-looking. However, if you are not using FedEx or another service at the time, there is no reason for you to get an invoice from them. But people tend to believe that and unfortunately, the minute user opens the infected file on the computer, the system is infected. If the machine is on the network belonging to a company, multiple devices can easily get infected at once.
