Researchers have just spotted a malicious Word document that spreads a new cross-platform malware. This cyber infection aims at both Windows and Mac OS X computers. Thus, this discovery might mark a revolution in malware distribution techniques. Indeed, while people can also be infected with ransomware thru fake alerts and infected websites, from the beginning the most popular distribution method was and still is malicious spam emails that include obfuscated documents. The success of these campaigns has already shown such viruses as Cerber, Zzzzz, Matrix, Spora and thousands of others. Hackers benefit from the naive computer users who still believe that Word documents cannot cause any harm. Obviously, it’s not true. Well, for a while Mac users could have felt safe because ransomware developers mostly aimed at Windows users. Thus, this situation has just changed.
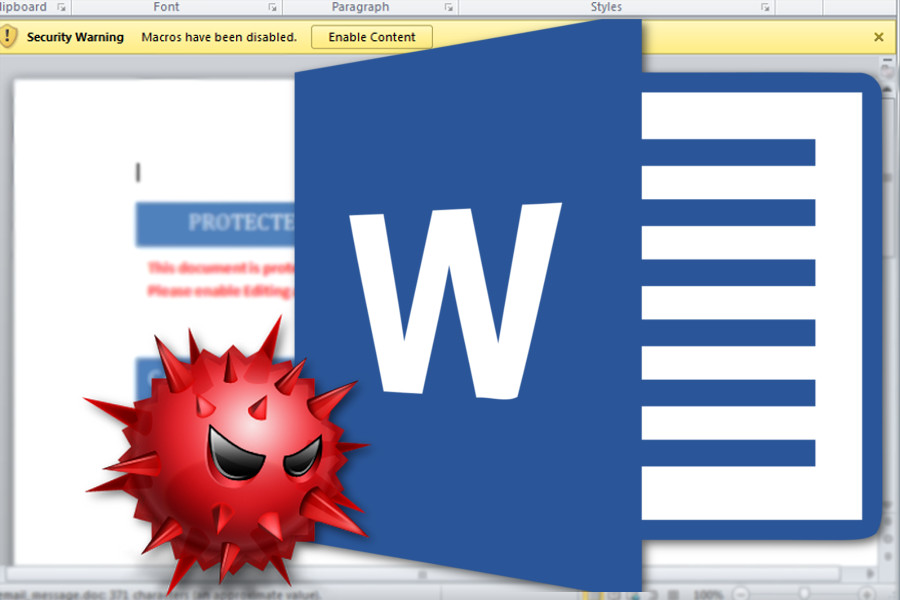
On March 16, researchers from Fortinet spotted a malicious MS Word documents spreading malware on both Windows and Mac OS X. This discovery might highlight the trend of creating cross-platform viruses because it allows cyber criminals to expand their target field. Thus, it doesn’t matter whether you use Microsoft or Apple product, chances to catch this malware are equal. However, if you won’t rush to open a Word document attached to a suspicious email, you can avoid this horrible cyber threat. Researchers exposed that this recently discovered file is designed to execute Visual Basic for Applications (VBA) code. People, who are tricked into opening it, are asked to enable Macro content. Indeed, this abominable trick has been used by many ransomware viruses. Though, if a person allows macros, the malicious code is executed and activates the malicious script.
The malicious script us based on modified version of Meterpreter and acts differently based on the affected computer’s operating system. Thus, once it is activated, it checks whether it infiltrated Mac or Windows OS, and decides which path to choose. Talking about Windows devices, it seems that malware only attacks the 64-bit version of the operating system and uses PoweShell scripts to launch the assault. Meanwhile, on Mac OS the malware uses a Meterpreter version that is written in Python. Developers chose a smart strategy because Python script is run by default on Mac OS X. As a result, malware gets full control of the attacked computer.
The only way to protect your Mac or Windows machine from this extortionist is to learn to identify malicious email attachment. This Word file might try to be a useful notification from a friend, boss or some governmental authority. However, often there’s something wrong regarding the malicious email message. For example, there are typo or grammar mistakes in the message body. Fortunately, cyber criminals rarely are good in English. What is more, before opening email attachments, you should also check the information about the sender and look at his or her email address. If you have some suspicions that something is wrong with this email, do not open this document!
