Data encryption for Zenis ransomware virus is not enough
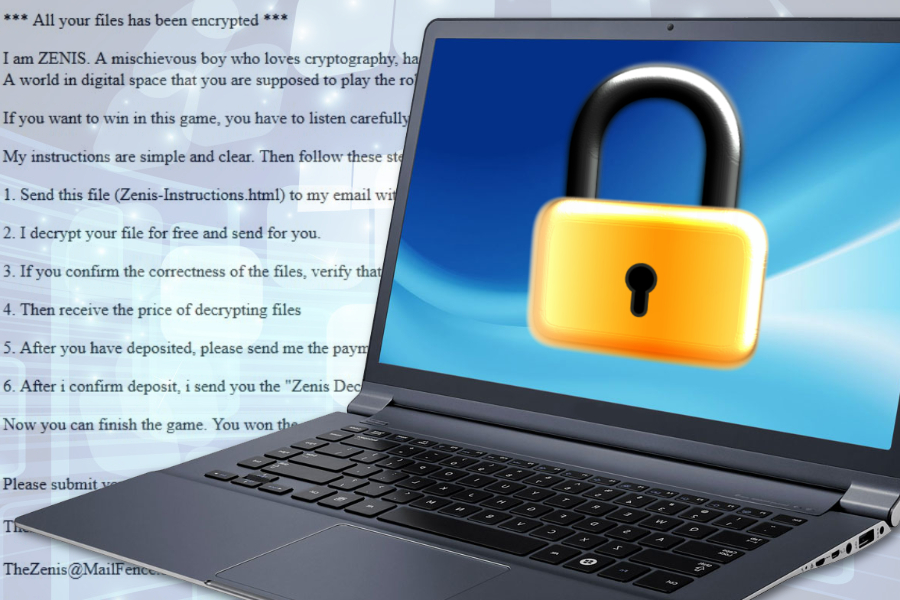
Zenis is a brand new ransomware virus that recently caught researcher’s eye. The virus seems similar to other file-encrypting malware. However, it’s distribution method is quite a mystery. Additionally, author of the virus uses a quite playful ransom note and invites victims to play a game.
However, this ransomware game means that users have to contact cyber criminals and pay the demanded sum in Bitcoins in order to obtain Zenis decryptor and a private key to unlock encrypted files. Security experts warn that playing this game is not a good idea.
The ransomware is capable of deleting Shadow Volume Copies, clear event logs, and disables startup repair to make data recovery complicated. However, deletion of backups is not enough. Malware also three times overwrites files that are associated with backups and finally deletes them.
Indeed, author of malware enjoys playing programming games and coding. However, he (or she) is not as successful of virus researcher who discovered how to recover files without paying the ransom.
The operation and features of Zenis virus
Researchers still cannot find any other ways how ransomware is being distributed. The only discovered method is Remote Desktop services. However, it’s doubtful that Zenis is being spread in only one way.
However, on the affected machine malware starts looking for targeted files for the encryption. It aims at most popular file-types. Ransomware uses AES cryptography, appends Zenis-<2_chars>. file extension, and can rename files with a random string of 64 characters.
As we have already mentioned, the malware then deletes backups and delivers a ransom note where victims are asked to send the ransom note (Zenis-Instructions.html) and one encrypted file to one of the following emails:
The hacker will respond with decrypted file and the size of the ransom that needs to be paid for Zenis decryptor. According to the criminal, when the user gets a private decryption key, the game is over; the victim wins.
However, paying the ransom is not recommended and needed. Transferring Bitcoins might lead to money loss. You might never get a chance to use it. Though, the more important part is that ransomware is decryptable.
A reminder how to protect yourself from ransomware attack
Zenis ransomware is one of those cyber threats that spread via poorly protected or insecure Remote Desktop services. Therefore, it’s crucial to set strong passwords, limit user access, use VPN connection and do not keep devices connected directly to the computer.
However, it’s still unknown if other methods are used in ransomware’s distribution. Besides, there are hundreds of other cyber threats spreading that you do not want to meet as well. Though, we want to remind these ransomware precautions tips:
- do not rush opening spam emails and stay away from their attachments;
- avoid downloading software from torrents and other unknown file-sharing sources;
- install programs only from the official download websites;
- stay away from aggressive ads, especially those who ask to install available updates.
However, you should also install reputable antivirus software and keep it updated. Keep in mind that having a security program installed does not mean that your device and data is fully protected. You have to follow safe browsing practices. Additionally, we highly recommend creating data backups. They will be very helpful in case of the cyber attack.
